My flowbies! I want to trigger a Flow based on someone being added to an Azure AD Group. This doesn’t appear to be possible currently, as the Azure AD connector has no triggers. Am I correct?
Andrew Bibby
Hold my beer
Microsoft Graph API contains the subscription feature where you can create subscriptions where a listener application receives notifications when the changes occur in the specified resource.
The process involves the following steps:
- Create the notification endpoint Flow
- Create an app in Azure AD
- Create a subscription
Let’s dig in.
Notification endpoint Flow
Creating a subscription requires a notification endpoint that must satisfy certain validation requirements, namely return a validationToken passed as a query parameter.
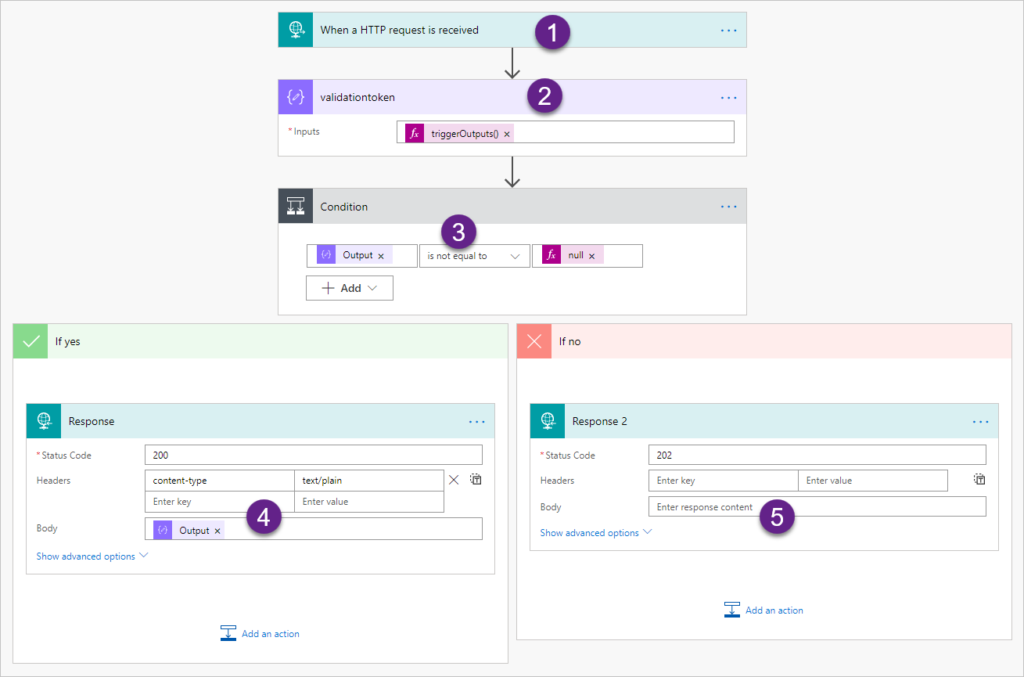
- Use HTTP request as a trigger. When the flow is saved, the trigger will contain a unique URL that we will need later.
- validationToken expression is triggerOutputs()?[‘queries’]?[‘validationToken’]. queries gives us access to the query string and then straight to the validationToken.
- When the token is passed as a query parameter, we are in the validation stage, actual notifications won’t have the parameter. So here we split our execution.
- We are asked to validate. As per requirements, return the token value in the plain text body. Flow takes care of all the required decoding.
- We are receiving a notification. For now we simply quickly return 202 response (Accepted). (If Microsoft Graph does not receive a 2xx code, it will retry the notification).
App in Azure AD
Creating app in Azure AD is very straightforward – just follow the documentation. Since we are subscribing to the group, we need to add Group.ReadAll permission for Graph API.
Subscriber Flow
I wish I could claim the technique of creating a subscription using Flow but the formidable John “Flow Ninja” Liu described the technique over a year ago :O. Just follow the steps and you’ll be all set. For a change, I decided to use Postman.
The easiest way to deal with authentication is to create a collection and set all requests within the collection to inherit the authentication token.
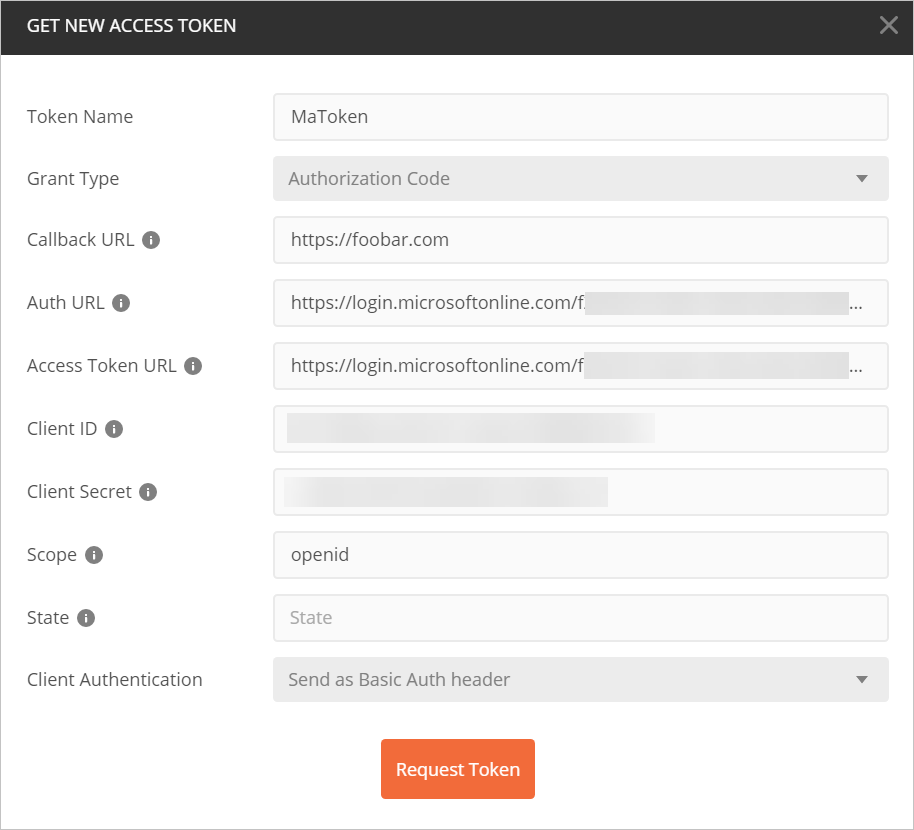
You’ll find all of the parameters in the app properties in Azure AD. And yes, callback URL does not really matter here but it’s required.
Once Postman has a token, sending request to subscribe to groups changes is a breeze:
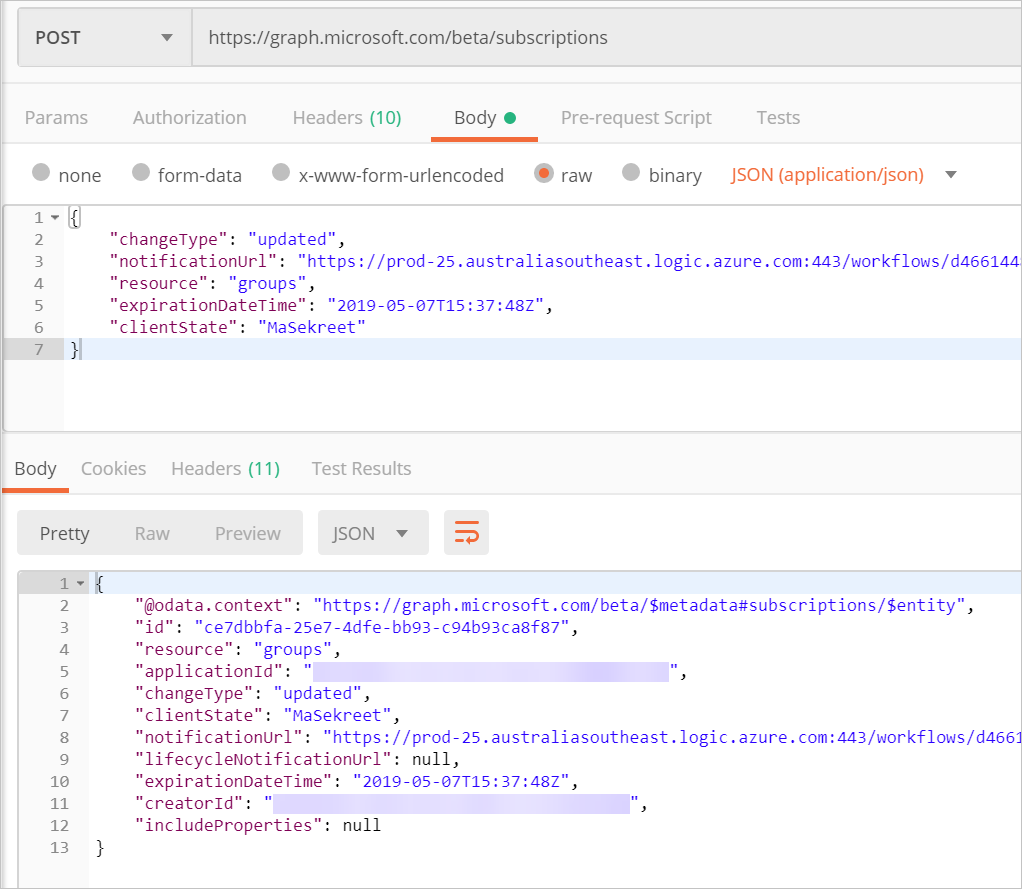
You need to use Flow URL from step 1 as a notificationUrl, and set expirationDateTime to something in the future but not too far (less than 3 days). Note that times are in UTC.
Testing
After adding a user to one of the groups in Azure AD, you’ll see two
(hopefully) successful runs for the notification Flow. First one is a validation run (you can drill into it and check the validation token that was passed in). Second one is the real McCoy containing the following data in HTTP request body:
[
{
"changeType": "updated",
"clientState": "MaSekreet",
"resource": "Groups/deadbeef-dead-beef-dead-beef00000075",
"resourceData": {
"@odata.type": "#Microsoft.Graph.Group",
"@odata.id": "Groups/deadbeef-dead-beef-dead-beef00000075",
"id": "deadbeef-dead-beef-dead-beef00000076",
"organizationId": "deadbeef-dead-beef-dead-beef00000077",
"eventTime": "2019-05-07T11:08:15.4245258Z",
"sequenceNumber": 636928240954245200,
"members@delta": [
{
"id": "deadbeef-dead-beef-dead-beef00000088"
}
]
},
"subscriptionExpirationDateTime": "2019-05-07T15:37:48+00:00",
"subscriptionId": "deadbeef-dead-beef-dead-beef00000069",
"tenantId": "deadbeef-dead-beef-dead-beef00000096"
},
{
"changeType": "updated",
"clientState": "MaSekreet",
"resource": "Groups/deadbeef-dead-beef-dead-beef00000075",
"resourceData": {
"@odata.type": "#Microsoft.Graph.Group",
"@odata.id": "Groups/deadbeef-dead-beef-dead-beef00000075",
"id": "deadbeef-dead-beef-dead-beef00000076",
"organizationId": "deadbeef-dead-beef-dead-beef00000077",
"eventTime": "2019-05-07T11:08:15.4245258Z",
"sequenceNumber": 636928240954245200
},
"subscriptionExpirationDateTime": "2019-05-07T15:37:48+00:00",
"subscriptionId": "deadbeef-dead-beef-dead-beef00000069",
"tenantId": "deadbeef-dead-beef-dead-beef00000096"
}
]
That’s a lot to digest but members@delta is the magic data that tells us that a user has been added to the group. I’ll save digesting this json for another day.
Here you go, Andy!
Cover photo by Lance Anderson
 of the
of the
[…] Subscribe to AD changes using Flow […]
What does it mean when a user is added to a group, but I don’t get the “members@delta” – it doesn’t even exist in the request? I’ve been trying to figure it out for weeks now…